While the Lightning Network significantly enhances the scalability and efficiency of the Bitcoin blockchain, it isn’t without its unique set of challenges. One such issue that poses a considerable threat to its users is the occurrence of routing attacks in the Lightning Network. This article aims to unravel the complexities of these attacks, including their various types, and offer insights on how to identify and mitigate them effectively.
Understanding Routing Attacks in the Lightning Network
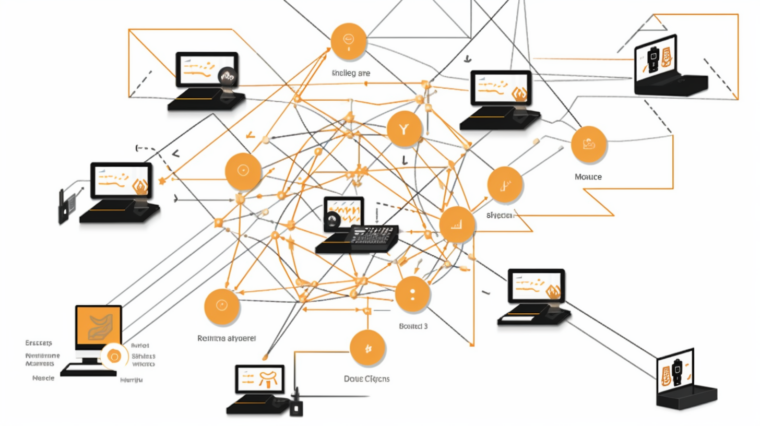
The Lightning Network, a layer-2 scaling solution for the Bitcoin blockchain, has brought about swift and cost-effective transactions by establishing a network of payment channels. However, it is not immune to potential security threats such as routing attacks, which involve users exploiting weaknesses in the routing system for personal gain. A common example of a routing attack is when a participant intentionally sets high routing fees, making it costly for others to route their payments through that participant’s channels, thereby impeding the Lightning Network’s ability to route payments effectively and affordably.
The Mechanism of Routing Attacks
Malicious users employ a myriad of strategies to exploit vulnerabilities or disrupt the Lightning Network’s payment routing system. Tactics include imposing exorbitant routing costs, spreading false information or errors across the network, and even conducting probing attacks to gain insights into the network architecture and user behavior. These deceptive actions can compromise the Lightning Network’s reliability and usability, making it crucial for developers and users to be vigilant and proactive in enhancing network security.
Common Types of Routing Attacks in the Lightning Network
There are several types of routing attacks that users should be aware of:
- Routing fee sniping: In this attack, a rogue node sets excessive routing fees for a payment channel it controls, deterring users from using the Lightning Network.
- Probabilistic payment fraud: Here, a malicious node falsely claims a successful payment was unsuccessful, reducing the network’s efficiency.
- Channel jamming attacks: A hostile actor deliberately locks up the liquidity in a payment channel, making it unavailable for legitimate users.
- Balance manipulation: A malicious node intentionally creates an imbalanced channel, disrupting the network’s operations.
- Route flapping: In this attack, a rogue node frequently changes its channel restrictions or fee structures, making it hard for others to find reliable payment channels.
- Sybil attacks: A rogue user sets up numerous fictitious nodes in the network, potentially misleading routing algorithms or executing other attacks.
- Onion routing attacks: A malicious node may try to de-anonymize a transaction by examining the routing data if it is part of the route, compromising the privacy of the sender, receiver, and the amount transferred.
Identifying and Avoiding Routing Attacks
Identifying routing attacks can be challenging as they often involve bad actors manipulating payment routing for personal gain. However, these attacks typically aim to disrupt the network’s functionality or unfairly profit from routing fees. They can manifest as unexpected payment failures, sudden changes in channel liquidity, or unforeseen routing fees.
Tools for network surveillance, watchtowers, route selection, and node behavior analysis can help detect these malicious behaviors. For instance, watchtowers designed to monitor suspicious activities can broadcast penalty transactions and scrutinize the blockchain for potential attempts to close the channel. Users can also improve their ability to detect routing threats by actively participating in the Lightning Network community and learning from previous attacks.
As you dive deeper into the world of cryptocurrencies, platforms like cryptoview.io can provide valuable insights and tools to monitor your investments and stay updated on the latest trends. This knowledge, coupled with a vigilant approach, can go a long way in safeguarding your transactions from potential routing attacks.
Invest in your crypto security with cryptoview.ioEnsuring protection against routing attacks is vital for maintaining the integrity and security of the Lightning Network. This can be achieved by selecting trusted nodes, diversifying routing paths, regularly monitoring channel activity, and keeping up with the latest software updates. By implementing these measures, users can fortify their defenses against routing attacks and foster a more secure environment for Lightning Network transactions.